SHA‑256: The Blender That Even Quantum Chef Can’t Reverse
Discover how mathematics secures Bitcoin. Explore SHA-256, mining mechanics, and why quantum computing doesn't spell the end for crypto's future.

In this article, we’ll break down the cryptographic foundations that protect Bitcoin, and explore whether quantum computers truly threaten its future.

Critics often point to the rise of Quantum Computing as a potential death blow to this security model, calling it the "End of Crypto." But to understand if Bitcoin can survive the future, we must first understand the digital machinery that keeps it running today.
What is SHA-256 and why does Bitcoin use it?
SHA-256 stands for Secure Hash Algorithm, 256-bit. It was designed by the National Security Agency (NSA) and published in 2001. Despite its origins, it is open-source, meaning anyone can inspect the code to ensure there are no backdoors.

At its core, SHA-256 is a "one-way" function. In simple terms, it is a digital grinder. You can put anything into it: a single letter, a password, or the entire Library of Congress, and it will output a unique string of 64 hexadecimal characters (numbers 0-9 and letters A-F).
The "256" refers to the length of the output in bits. This number is massive. SHA-256 offers about $1.16 \times 10^{77}$ possible combinations, roughly equal to the estimated number of atoms in the universe 🤯. Guessing a specific hash is statistically impossible within the timeframe of our universe's existence.
SHA-256 is deterministic (the same input gives the same output) but unpredictable. This is called pseudorandom determinism: you can’t predict the output without running the function, yet it will always yield the same unique result for the same input.
It serves two main purposes in Bitcoin:
- Fingerprinting: It creates a unique identifier for every transaction and block.
- Mining: It provides the "puzzle" that miners must solve to secure the network.
Furthermore, Bitcoin actually uses Double-SHA-256 (hashing the data, then hashing the result again) when creating addresses. This adds an additional security layer built into its design specifically to prevent "length-extension attacks," where a hacker might try to append information to a hash without knowing the original input.
To understand why this hashing matters, let’s look at how it’s applied in Bitcoin’s core process.
The Avalanche Effect
The primary security feature of SHA-256 is something cryptographers call the Avalanche Effect.
In traditional record-keeping, if you change one number in a spreadsheet, only that cell changes. In Bitcoin, if you change a single bit of data in a transaction history, the entire hash changes completely.
Let’s look at an example:
- Input: "Bitcoin is secure"
- Output:
6b88c087247aa2f07ee1c5956b8e1a9f4c7f891a7413f7116120ef08d5711d4e
Now, let’s change just the last letter from an "e" to a "d".
- Input: "Bitcoin is securd"
- Output:
5f78c33274e43fa9de5659265c1d917e25c03722dcb0b7d2c63875324df79763
The two outputs look nothing alike. This property is vital. If a hacker tries to alter a transaction from five years ago to give themselves 100 BTC, the hash of that block changes. Because every block is connected to the next, the hash of the next block changes, and the next, all the way to the present day.
This avalanche property also ensures collision resistance, meaning it’s computationally infeasible for two different inputs to produce the same hash.
Think of SHA-256 like a blender, once something goes in, the output (hash) looks nothing like the original input, and you can’t reverse the process to recover the ingredients.
You would have to re-mine the entire history of Bitcoin from the point of the hack to the present. But who is doing this mining, and what makes it so expensive?
The Role of Miners
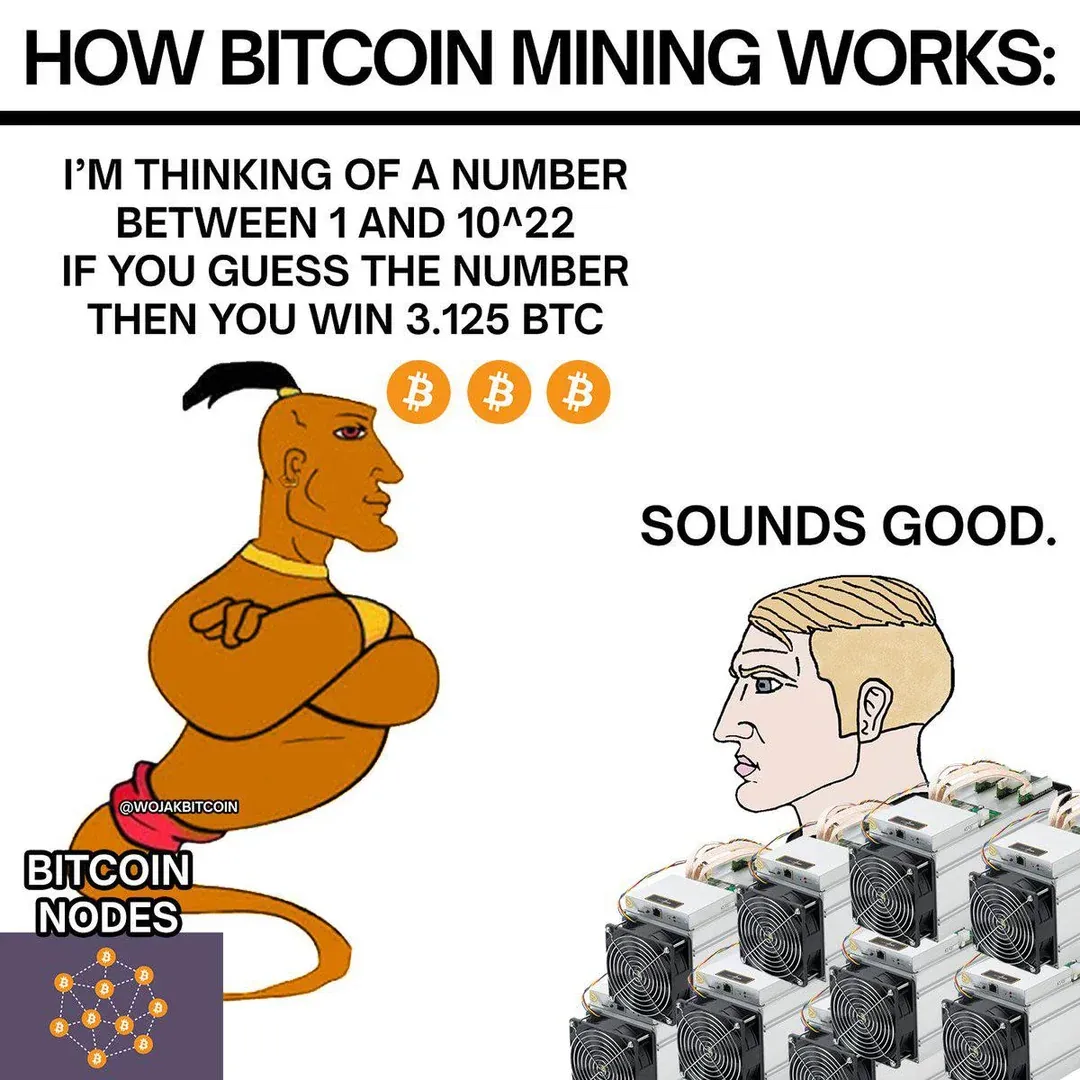
Mining is often misunderstood as "solving complex math problems." This phrasing suggests miners are doing calculus. They aren't. They are playing a global lottery of guess-and-check.
Miners take a batch of new transactions, combine them with the hash of the previous block, and add a random number called a Nonce (Number Used Once). They run this mixture through the SHA-256 algorithm. The goal is to find a resulting hash that starts with a specific number of zeros.
The Difficulty Adjustment
Because computer hardware gets faster over time, the network must ensure blocks aren't found too quickly. Bitcoin automatically adjusts its mining difficulty approximately every 2,016 blocks (about every two weeks) to maintain an average 10-minute block time, even as hardware improves. If more miners join, the puzzle gets harder; if they leave, it gets easier.

The Halving and the Difficulty Adjustment work together to keep Bitcoin stable during economic shocks. When a Halving cuts miner rewards in half, many miners may turn off their machines because they are no longer profitable, which slows down the network; the Difficulty Adjustment then detects this slowdown and automatically makes the mining puzzle easier.
Will Quantum Computers break Bitcoin?
This is the most common "FUD" (Fear, Uncertainty, and Doubt) circulating. The narrative suggests that once a powerful Quantum Computer is built, it will crack Bitcoin’s code instantly, draining everyone's wallets.
The reality is far more nuanced. Quantum attacks target specific types of mathematics; not every cryptographic process is equally vulnerable.
We need to distinguish between the two types of cryptography Bitcoin uses: Hashing (SHA-256) and Signing (ECDSA).
The Threat to SHA-256 (Mining and Block History)
Quantum computers use an algorithm called Grover’s Algorithm to speed up the search for data. Theoretically, this could help a quantum computer reverse-engineer a hash.
However, Grover’s Algorithm only provides a "quadratic" speedup. This means if you have a 256-bit security level, a quantum computer reduces it to 128-bit security. Currently, even if Grover’s algorithm achieved full efficiency, it would still require $2^{128}$ operations, still beyond any conceivable computer.
Bitcoin mining and the blockchain history are safe from quantum attacks.
The Threat to ECDSA (Private Keys)
This is the real vulnerability. Bitcoin uses the Elliptic Curve Digital Signature Algorithm (ECDSA) to generate public and private keys. This is what you use to sign a transaction to spend your money.
A different quantum method, Shor’s Algorithm, can theoretically derive a private key from a public key. However, breaking ECDSA with Shor’s algorithm would require 10–20 million error-corrected logical qubits operating continuously.
For context, current research prototypes have fewer than 2,000 physical qubits, which are far less stable than logical qubits.
How Bitcoin Defends Against the Future
Bitcoin has a built-in defense mechanism: Hashing Public Keys.
When you create a Bitcoin address, you don't share your Public Key. You share a Double-SHA-256 Hash of your Public Key. As we mentioned, SHA-256 is quantum-resistant.
Your Public Key is only revealed to the network the moment you send a transaction.
- Scenario A: You have Bitcoin in an address and you never move it. Your Public Key is not on the blockchain, only the SHA-256 hash is. A quantum computer cannot steal your funds.
- Scenario B: You send a transaction. Your Public Key is revealed. A quantum computer would have to crack your key in the 10 minutes before the transaction is mined into a block. Even if block confirmation took longer than 10 minutes, the computational gap remains enormous; no existing or near-term quantum device could complete that task.
But what if quantum technology leaps forward unexpectedly? Is Bitcoin stuck with its current code?
Can Bitcoin upgrade to survive a Quantum Future?
Yes. Bitcoin is software, not a static stone tablet.
The Bitcoin protocol can be upgraded through "Soft Forks" or "Hard Forks." Developers are already working on Post-Quantum Cryptography (PQC).

Two potential solutions include:
- Lamport Signatures: A different way of signing transactions that is resistant to quantum attacks but requires larger data sizes.
- Lattice-based algorithms: Algorithms such as CRYSTALS-Dilithium and Falcon: Both selected by NIST (U.S. National Institute of Standards and Technology) for post-quantum use, are being studied by Bitcoin developers for long-term integration.
- Taproot Upgrades: The recent Taproot upgrade already lays the groundwork for more flexible signature types (Schnorr signatures), which can be adapted for better security.

If a credible quantum threat emerges, the Bitcoin network would reach a 'consensus' to implement a new signature scheme. Users would simply move their funds from their old "vulnerable" addresses to new "quantum-secure" addresses. But this scenario would be a terrifying one for sure.
Conclusion
Bitcoin’s security is not an accident; it is a deliberate combination of economic incentives and cryptographic laws. SHA-256 serves as the shield, ensuring that history cannot be rewritten.
While technology advances and threats like quantum computing loom on the horizon, the architecture of Bitcoin allows it to adapt. The "FUD" surrounding its security usually stems from a misunderstanding of how difficulty adjustments and hashing actually work.

Connect with Bitfinity Network
Bitfinity Wallet | Bitfinity Network | Twitter | Telegram | Discord | Github
*Important Disclaimer: The information provided on this website is for general informational purposes only and should not be considered financial or investment advice. While we strive for accuracy, Bitfinity makes no representations or warranties regarding the completeness, accuracy, or reliability of the content and is not responsible for any errors or omissions, or for any outcomes resulting from the use of this information. The content may include opinions and forward-looking statements that involve risks and uncertainties, and any reliance on this information is at your own risk.
External links are provided for convenience, and we recommend verifying information before taking any action. Bitfinity is not liable for any direct or indirect losses or damages arising from the use of this information.









Comments ()